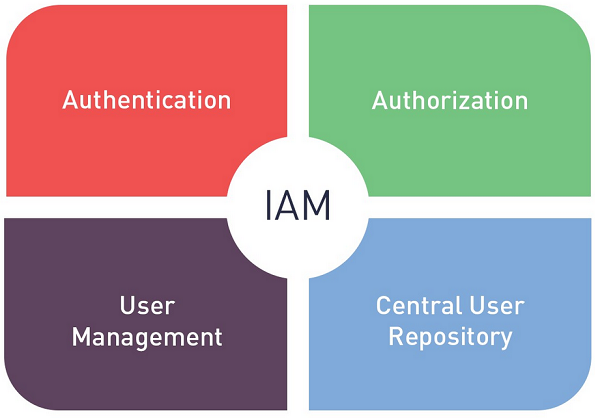
A modern, enterprise-grade Identity and Access Management platform is a complex, multi-service architecture designed to be the central authority for all digital identities and access policies. A complete Identity and Access Management Market Solution is not a single piece of software but an integrated suite of capabilities that work together to manage the full identity lifecycle. This end-to-end solution is composed of several key architectural pillars: a core identity directory, a robust authentication engine, a flexible authorization and policy engine, and a comprehensive governance and administration layer. Understanding the anatomy of this solution is essential to appreciating how these platforms provide the secure, scalable, and user-friendly foundation for the modern Zero Trust enterprise.
The foundation of any IAM solution is the core identity directory. This is the "single source of truth" where all the digital identities and their associated attributes are stored and managed. For many organizations, this is still a traditional on-premise directory like Microsoft Active Directory. However, the modern approach is a cloud-based, universal directory. This directory can store not only employee identities but also identities for customers, partners, and even non-human entities like applications and devices. It synchronizes with various other identity sources (like HR systems) and provides a single, unified profile for each identity, which is the essential foundation upon which all authentication and authorization decisions are made.
The next critical layer is the authentication engine. This is the component responsible for verifying a user's identity when they try to log in. A modern solution provides a wide range of authentication methods. This includes support for Single Sign-On (SSO) using open standards like SAML and OIDC, which allows a user to log in once and access many applications. The most important part of this engine is the Multi-Factor Authentication (MFA) capability. This provides a flexible policy engine that can require a second factor of authentication—such as a push notification to a mobile app, a one-time passcode, or a biometric check—based on the risk of the login attempt. A key trend is the move towards passwordless authentication, using standards like FIDO2 to provide a more secure and user-friendly login experience.
Finally, the entire system is governed by the authorization and administration layer. The authorization component is the policy engine that determines what a user is allowed to do after they have been authenticated. It enforces the principle of least privilege, granting access to specific applications and data based on the user's role, group, and other contextual attributes. The Identity Governance and Administration (IGA) component provides the tools for managing the identity lifecycle. This includes workflows for automated user provisioning (creating accounts for new hires) and de-provisioning (disabling accounts for leavers). It also includes tools for managing access requests, approvals, and periodic access certification campaigns, providing the essential auditability and control required for a secure and compliant enterprise.
Other Exclusive Reports: